Some HTTPS sites report the same invalid certificate after recent Nightly updates
Hello there,
After my Firefox Nightly updated a couple of days ago (I currently have 2017-07-20 build, but the issue came up earlier), some sites like github.com, amazon.com and pastebin.com stopped loading with the SEC_ERROR_UNKNOWN_ISSUER error.
Info from the Advanced button:
Peer’s Certificate issuer is not recognized.
HTTP Strict Transport Security: true HTTP Public Key Pinning: true
Certificate chain:
BEGIN CERTIFICATE-----
MIICATCCAWoCCQD1ui5gnJHbtDANBgkqhkiG9w0BAQUFADBFMQswCQYDVQQGEwJB VTETMBEGA1UECAwKU29tZS1TdGF0ZTEhMB8GA1UECgwYSW50ZXJuZXQgV2lkZ2l0 cyBQdHkgTHRkMB4XDTE0MTAxMzEyNDYwM1oXDTE0MTExMjEyNDYwM1owRTELMAkG A1UEBhMCQVUxEzARBgNVBAgMClNvbWUtU3RhdGUxITAfBgNVBAoMGEludGVybmV0 IFdpZGdpdHMgUHR5IEx0ZDCBnzANBgkqhkiG9w0BAQEFAAOBjQAwgYkCgYEAt4ka Npv6pBCK9BAVr8y7FgNkrvwtAOwfjR8HZwkHwk0xgbjt7UJQVvqdlTVOhEIscwVS KQAGrw9d0pfjRjgNZWNbw2KKfEjc5J4eByLnCrG0DtAfohgyLVppv8n5T0UgCH4A T3XPVLj/qdenv7ySbrNPdIq8TTlDVv+0Awsu8KcCAwEAATANBgkqhkiG9w0BAQUF AAOBgQBnYRFTWiLxrCbU3AQjLaEfGN6Kb1yf1Y2xxm/XkYPEoCN23zy3Yt3674KE lO3Z0TJv3pda+4WN41OnuYE1Vgatlhai/lgxJBfMkZ94IljnLs7uj5AfYQiffcx/ GVlxkEQXHDsyERWJmJjS/0swu7crz2O0Ip6IF30ILSBaRPBt3w==
END CERTIFICATE-----
The certificate is the same for all sites that stopped working. Firefox Nightly also says "The certificate expired on Wednesday, November 12, 2014, 3:46 PM."
Everything works fine when connected via TOR proxy. So I suspect my ISP. But I have no clue why it started happening right after one of the updates. The regular Firefox works fine, too.
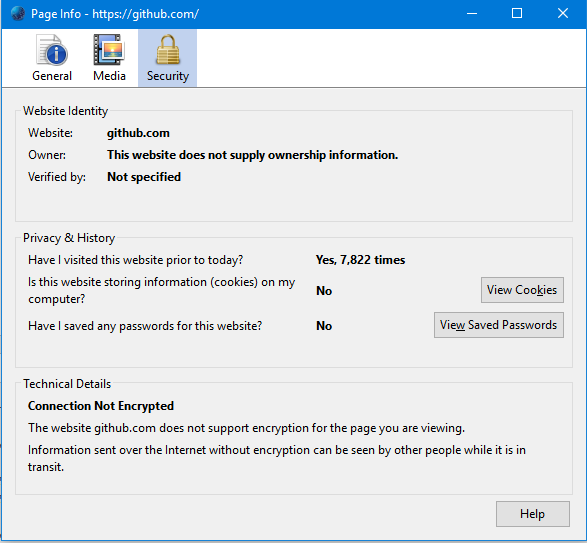
What's also weird is that "Page Info" window (accessible via the address bar icon) tells me I don't have any password nor cookies saved for github.com. In fact, I do have cookies saved for GitHub, I've just confirmed that at about:preferences#privacy
The page visit counter (located on in that same window) says I've visited GitHub 7,822 times, so the counter probably works.
Chosen solution
A little update on this. I've contacted one of the Firefox developers - the one who was working on the TCP Fast Open feature - told them about the issue, they're now aware of it. What's more, in current Nightly builds the problem is not present (even with TFO turned on).
I guess I can mark this as solved, at least now I have an idea of what was going on.
Thanks to cor-el and jscher2000 for support.
Read this answer in context 👍 1All Replies (20)
Whoops, the image didn't get added
That is an expired certificate.
Data:
Version: 1 (0x0)
Serial Number: 17706515877439069108 (0xf5ba2e609c91dbb4)
Signature Algorithm: sha1WithRSAEncryption
Issuer: C=AU, ST=Some-State, O=Internet Widgits Pty Ltd
Validity
Not Before: Oct 13 12:46:03 2014 GMT
Not After : Nov 12 12:46:03 2014 GMT
Subject: C=AU, ST=Some-State, O=Internet Widgits Pty Ltd
You can check the connection settings.
- Options/Preferences -> Advanced -> Network : Connection -> Settings
- https://support.mozilla.org/en-US/kb/Options+window+-+Advanced+panel
If you do not need to use a proxy to connect to internet then try to select "No Proxy" if "Use the system proxy settings" or one of the others do not work properly.
See "Firefox connection settings":
See also:
Thanks for the fast reply!
I switched to "No Proxy" but that didn't solve the problem.
I'd go straight to my ISP forums if this didn't start hapenning right after the browser update.
How about other browsers on your system? If you visit one of those problem sites in the other browser and check the certificate information, does it show the certificate as that expired one, or is the problem limited to Firefox?
At least one site suggests that issuer's certificates have been used to sign unwanted software: https://www.reasoncoresecurity.com/signer-internet-widgits-pty-ltd-009dd8bc177abb2f73.aspx
Could you test in Firefox's Safe Mode? In Safe Mode, Firefox temporarily deactivates extensions, hardware acceleration, and some other advanced features to help you assess whether these are causing the problem.
If Firefox is not running: Hold down the Shift key when starting Firefox.
If Firefox is running: You can restart Firefox in Safe Mode using either:
- "3-bar" menu button > "?" button > Restart with Add-ons Disabled
- Help menu > Restart with Add-ons Disabled
and OK the restart.
Both scenarios: A small dialog should appear. Click "Start in Safe Mode" (not Refresh).
Any improvement? (More info: Use Troubleshoot Mode in Firefox)
Thanks for your reply!
Internet Explorer shows the correct certificate for github.com, signed by DigiCert.
Restarted in Safe Mode - the dialog appeared, I'm in Safe Mode now. But the problem persists.
Forgot to mention, I've performed a scan with Kaspersky Virus Removal Tool (their free service), targetting boot locations and memory. Nothing showed up.
Google Chrome and the main-channel Firefox also show the correct certificate from DigiCert.
Modified
Hmm, I don't normally use Nightly, but I updated it just now and don't notice any new issues with Github or Amazon.
Do you have any exceptions saved for these sites in the Certificate Manager?
"3-bar" menu button (or Tools menu) > Options
In the left column, click Advanced. Then on the right side, click the Certificates mini-tab along the top. Then click the "View Certificates" button.
This should open the Certificate Manager. Click the "Servers" tab. Ignore the ones for "*" and check for any servers matching problem sites.
Well, I'm pretty confident that I've never added exceptions to amazon.com as I only started using their site this June.
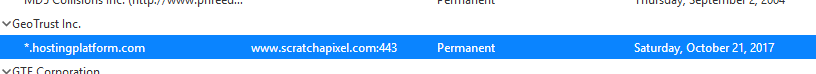
Okay, I've made my way to the Certificate Manager window, though a bit differently.
Anyways, here's the only non-wildcard certificate there:
Perhaps try some other malware cleaning tools. The support article lists several that are either free or have a free trial.
Tried Microsoft Safety Scanner and "SUPERAntiSpyware Portable Scanner Personal Edition" with no luck. Well, the latter has found 462 "threats" - tracking cookies.
I've googled that base64 string of the certificate:
- https://gist.github.com/blacklion/49dbb5c16653e3c3877db6012893e593 and https://juick.com/blacklion/2840429
- https://gist.github.com/sigsergv/5f1aeb063b2600516997
Already tried to contact blacklion to get more info on that certificate, but judjing from their discussion at juick.com, blacklion got that certificate for smarkets.com, which (as reported by other users in that thread) was affected by our Internet censorship a the time.
Couldn't find sigsergv's contact info, but he lives in Novosibirsk.
It has to do something with Russian Internet regulation ^W censorship law, but... Why only Nightly? And only after the update? ><
I don't know what to think now.
Oh, and blacklion mentioned that he runs "FreeBSD with read-only filesystem", so... I guess I might stop searching for malware on my machine now?
Thank you for your support guys
See also: https://www.google.com/search?q=%22Internet+Widgits+Pty+Ltd%22
Do a malware check with several malware scanning programs on the Windows computer.
Please scan with all programs because each program detects different malware. All these programs have free versions.
Make sure you update each program to get the latest version of their databases before doing a scan.
- Malwarebytes' Anti-Malware:
http://www.malwarebytes.org/mbam.php - AdwCleaner:
http://www.bleepingcomputer.com/download/adwcleaner/
http://www.softpedia.com/get/Antivirus/Removal-Tools/AdwCleaner.shtml - SuperAntispyware:
http://www.superantispyware.com/ - Microsoft Safety Scanner:
http://www.microsoft.com/security/scanner/en-us/default.aspx - Windows Defender:
http://windows.microsoft.com/en-us/windows/using-defender - Spybot Search & Destroy:
http://www.safer-networking.org/en/index.html - Kasperky Free Security Scan:
http://www.kaspersky.com/security-scan
You can also do a check for a rootkit infection with TDSSKiller.
- Anti-rootkit utility TDSSKiller:
http://support.kaspersky.com/5350?el=88446
See also:
- "Spyware on Windows": http://kb.mozillazine.org/Popups_not_blocked
Note that in current Nightly releases with the new about:preferences design you can find the certificates under the Privacy & Security tab at the bottom of this list (Security -> Certificates).
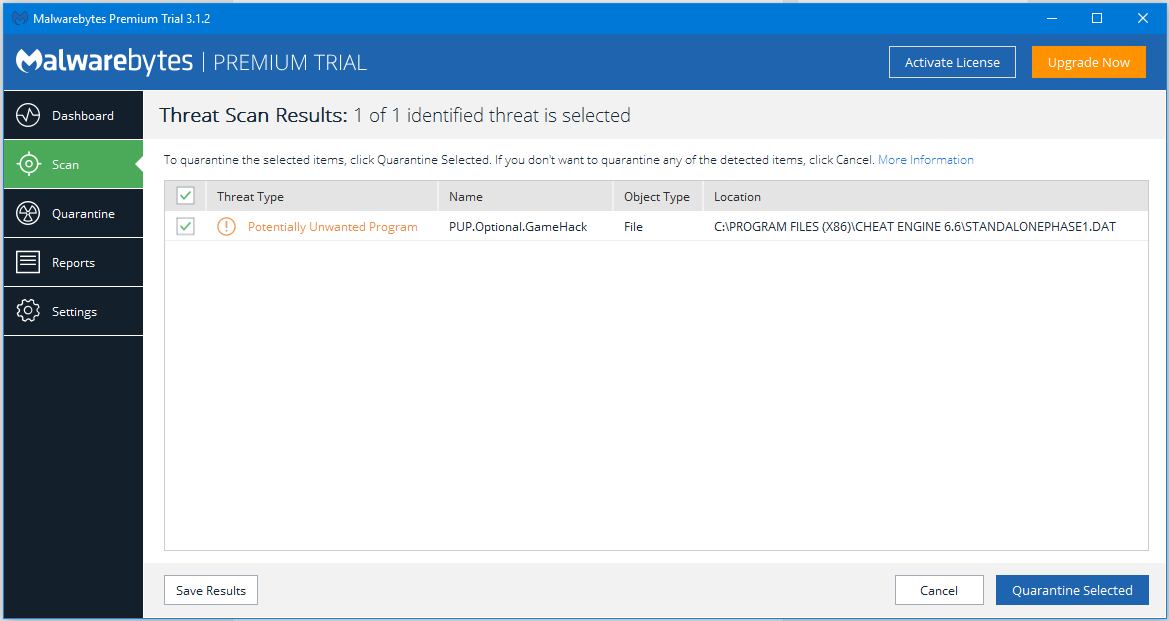
- Malwarebytes Premium Trial has only detected CheatEngine as a PUP;
- Malwarebytes AdwCleaner hasn't detected anything;
- SuperAntispyware scan results were described in my previous post;
- Microsoft Safety Scanner scan results were described in my previous post;
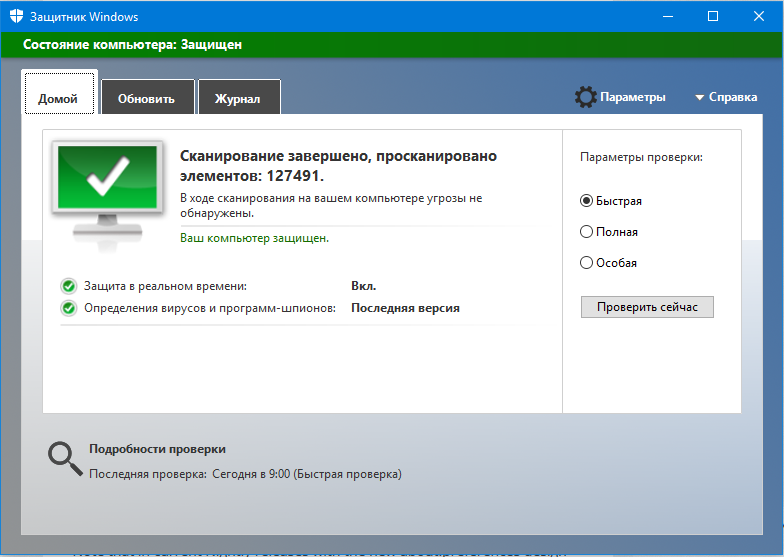
- Windows Defender hasn't detected anything;
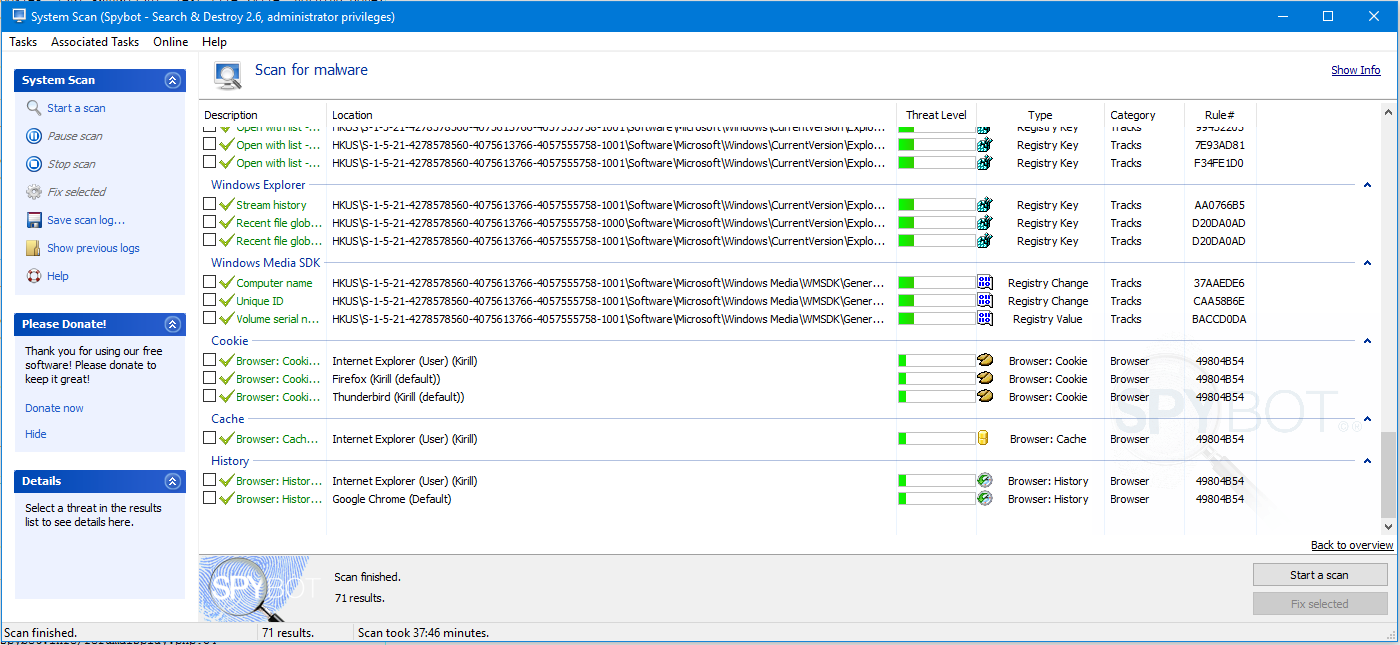
- Spybot Search & Destroy has only detected tracking cookies and 7-Zip context menu entries;
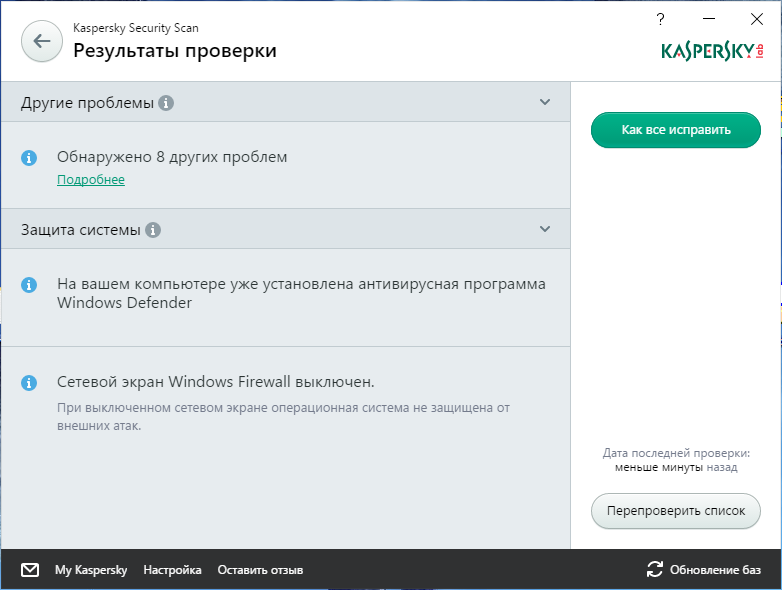
- Kasperky Free Security Scan has only detected 8 "other problems" like "non-standard IE start page" or "turning IE reports on may leak personal information"';
- Kaspersky TDSSKiller hasn't detected anything;
I've just installed the latest Nightly on another machine in my local network, and github.com now reports invalid certificate there, too.
As with my main desktop, other browsers (including Firefox) load these sites without problems.
I've tried a different ISP (LTE), and these sites started loading in Nightly just fine. I guess it's just some magic incompatibility between one of the latest Nightly updates and my ISP then.
Could you change your user agent on Nightly to the release UA to see whether that bypasses the problem? Here's how:
(0) Select and copy this new preference name:
general.useragent.override
(1) In a new tab, type or paste about:config in the address bar and press Enter/Return. Click the button promising to be careful.
(2) In the search box above the list, type or paste usera and pause while the list is filtered
Assuming you do not see that preference:
(3) Right-click a blank area of the page, New > String, then paste the preference name and click OK, then enter any text temporarily and click okay
Once the preference exists:
(4) Select and copy this value:
64-bit Firefox on 64-bit Windows 10: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:54.0) Gecko/20100101 Firefox/54.0
32-bit Firefox on 64-bit Windows 10: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:54.0) Gecko/20100101 Firefox/54.0
(5) Double-click the general.useragent.override preference and paste the new value, then click OK
You can test that the new value is sent using https://www.jeffersonscher.com/res/jstest.php (red text)
To clear the override later, right-click the preference and choose Reset.
I did what you proposed.
Unfortunately, faking Firefox 54 didn't solve the problem.
I also tried setting my User-Agent to the one from Edge. Didn't work either.
I've looked through the commit history on Mozilla's GitHub mirror, and got interested by this commit: https://github.com/mozilla/gecko-dev/commit/02da186004ba9d352f746304efea0c022ba78f69
network.tcp.tcp_fastopen_enable's default value in my current Nightly is true. If I switch it to false, the problem dissapears.
However, when I switch it back to true, the problem is still not present. I need to restart Nightly (with that pref set to true) for it to come back again.
Actually the correct commit is probably this: https://github.com/mozilla/gecko-dev/commit/3d59bf74c826d8c75d427104508397aa172055ed It's part of Bug 1363372
Chosen Solution
A little update on this. I've contacted one of the Firefox developers - the one who was working on the TCP Fast Open feature - told them about the issue, they're now aware of it. What's more, in current Nightly builds the problem is not present (even with TFO turned on).
I guess I can mark this as solved, at least now I have an idea of what was going on.
Thanks to cor-el and jscher2000 for support.